

Cybersecurity researchers from Leviathan Security have flagged a potentially major security concern around VPN services. The team recently uncovered a vulnerability that forces almost all such...


APT42, an Iranian state-sponsored hacking group also known as Charming Kitten or Yellow Garuda has been spotted impersonating journalists from popular mainstream media titles in an...


The identity of the leader of one of the most infamous ransomware groups in history has finally been revealed. On Tuesday, a coalition of law enforcement...


The website of ransomware hackers LockBit, which was seized by police and shut down, has relaunched. However, it wasn’t the hackers that propped it back up,...


DeleteMe is one of the best data removal services out there right now, helping you keep your personal data from data brokers and other internet parties...


Businesses have gotten a lot better at spotting cyberattacks recently, but they still struggle to address the problem. As a result, they still suffer the consequences....


Multiple hacking collectives are been actively using Microsoft Graph API to hide their communications with command & control (C2) infrastructure hosted on Microsoft cloud services, cybersecurity...


North Korean state-sponsored threat actors are abusing misconfigurations in DMARC to send convincing phishing emails and gather vital intelligence from Western targets, officials have warned. A...
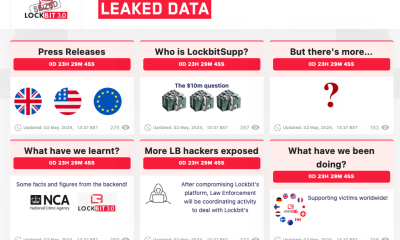

An international coalition of police agencies have resurrected the dark web site of the notorious LockBit ransomware gang, which they had seized earlier this year, teasing...


Microsoft has announced a new, upcoming feature, that aims to solve a decades-old conundrum with DNS security. The feature is called ZTDNS, or Zero Trust Domain...


In a bold move addressing some major cybersecurity concerns that have plagued the company in recent months, Microsoft has linked executive compensation to the company’s security...


Hackers have been observed targeting Mac devices running on both Intel and ARM silicon with brand new infostealer malware. Mac security provider Kandji discovered the malware...

We now know how APT28, a known Russian state-sponsored threat actor, managed to compromise multiple email accounts belonging to the Executive Committee of the German Social...
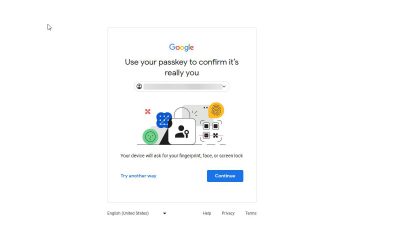

Google is extending its passkeys work in a bid to boost security across the world ahead of a series of major elections, including the US presidential...


Whether you want to browse the web anonymously, stream geo-locked content, or secure your data while using public Wi-Fi, there are many reasons why you might...


Microsoft has just unveiled the next step in its major cybersecurity overhaul, and that is to hire security executives for different product groups. Following a string...


The ransomware attack that has engulfed U.S. health insurance giant UnitedHealth Group and its tech subsidiary Change Healthcare is a data privacy nightmare for millions of...


The U.S. Cybersecurity and Infrastructure Security Agency (CISA), and the Federal Bureau of Investigation (FBI), published a new joint security alert earlier this week, urging software...


Former business smartphone company turned security firm, Blackberry, has lifted the wraps of its new AI-driven threat detection and response tool. CylanceMDR, the company’s new Managed...


Cybersecurity researchers from Microsoft found a way for Android malware to overwrite files in another, legitimate application’s home directory. In theory, threat actors could use this...


A controversial push by European Union lawmakers to legally require messaging platforms to scan citizens’ private communications for child sexual abuse material (CSAM) could lead to...
Installing Surfshark on your Fire Stick is a surefire way to get more out of both your VPN subscription and any streaming services you pay for....


Ahead of the U.S. presidential election, Google is bringing passkey support to its Advanced Protection Program (APP), which is used by people who are at high...


E-signature service providers DropBox Sign suffered a cyberattack recently, in which hackers stole some seriously sensitive customer information. As per the data breach notification published on...


Digital fraud detection company BioCatch has a new majority shareholder: U.K-based private equity firm, Permira, is acquiring shares in the company “primarily” from existing investors including...

When hackers find a vulnerable router, they compromise it by installing malware that grants persistence, the ability to run distributed denial of service (DDoS) attacks, hide...


Cybersecurity researchers from JFrog recently discovered three malicious campaigns in Docker Hub – Docker’s cloud-based registry service for storing and sharing container images. These campaigns contained...


Two months after hackers broke into Change Healthcare systems stealing and then encrypting company data, it’s still unclear how many Americans were impacted by the cyberattack....


UnitedHealth Group chief executive officer Andrew Witty told senators on Wednesday that the company has now enabled multi-factor authentication on all the company’s systems exposed to...


Developers have a problem. It used to be the case that only large enterprises needed to worry themselves with security, but today, every startup is capable...


In 2017, Jyoti Bansal co-founded San Francisco-based security company Traceable alongside Sanjay Nagaraj, a former investor. With Traceable, Bansal — who previously co-launched app performance management...


Island, the secure browser company, may be the most valuable startup that you have never heard of. The company, which is putting the browser at the...


Island, the enterprise browser company, may be the most valuable startup that you have never heard of. The company, which is putting the browser at the...


The U.S. Federal Communications Commission said on Monday that it is fining the four U.S. major wireless carriers around $200 million in total for “illegally” sharing...


Chinese state-sponsored actors are apparently mapping out the entire internet, but it’s hard to determine why. Some media speculate that it might be in preparation for...


To break into Change Healthcare’s IT systems, hackers abused a vulnerability in a Citrix remote desktop access product. This is according to Andrew Witty, Chief Executive...


Entrepreneurs Al Yang and Adar Arnon met at Harvard Business School and quickly realized that they had an interest in common: cybersecurity. “We’ve witnessed an evolving...


An American debt collection agency suffered a data breach in late February, losing sensitive data belonging to almost two million people. Earlier this week, Financial Business...

The ransomware gang that hacked into U.S. health tech giant Change Healthcare used a set of stolen credentials to remotely access the company’s systems that weren’t...


Canadian retail pharmacy chain London Drugs experienced a cyber-incident which forced the company to temporarily shut down its stores across Western Canada. On Sunday night, the...


Fake USPS websites, designed to steal people’s sensitive information and payment data through phishing, get almost as much traffic as the actual USPS website. During the...


RockAuto, a car parts dealer operating across North America, has been in a one-sided battle recently as it tries to remove a counterfeit app impersonating the...


Software developers are being targeted, once again, by fake job ads. The goal of the newly observed campaign is the same as the ones seen before...


Identity and access management company Okta says it is facing an “unprecedented” scale of credential stuffing attacks, looking to breach user accounts of its online services. ...


Spy.pet, a website that offered billions of Discord chat logs for sale, has been taken offline by the chat app provider. Discord accounts associated with the...


Despite security experts constantly warning about the risks of reusing passwords, a shockingly high number of people still do just that – and to make matters...


Millions of devices are still connected to the PlugX malware, despite its creators abandoning it months ago, experts have warned. Cybersecurity analysts Sekoia managed to obtain...


A critical vulnerability recently discovered in a popular WordPress plugin, is being actively abused in the wild, researchers have said, with hackers potentially able to use...

Apple’s App Store isn’t always as trustworthy as the company claims. The latest example comes from RockAuto, an auto parts dealer popular with home mechanics and...

Apple’s App Store isn’t always as trustworthy as the company claims. The latest example comes from RockAuto, an auto parts dealer popular with home mechanics and...


Darktrace is set to go private in a deal that values the U.K.-based cybersecurity giant at around $5 billion. A newly-formed entity called Luke Bidco Ltd,...


Microsoft CEO Satya Nadella has revealed plans for the tech giant would increase its commitment to security after being hit by a series of high-profile attacks...


U.S. health conglomerate Kaiser is notifying millions of its members of a data breach earlier this month. In a legally required notice filed with the U.S....


IT security pros are not the only ones with sandboxes and honeypots to test malware in, as hackers are doing the same – in developing parts...


Rubrik shares hit the New York Stock Exchange Thursday debuting at $38 a share. The cybersecurity company priced it shares at $32 apiece Wednesday night, just...
A popular phone tracking app was found to be leaking sensitive data on millions of its users. A security researcher named Eric Daigle discovered the flaw...


Network monitoring and security solution Progress Flowmon was found to be carrying a maximum-severity vulnerability which could allow threat actors to escalate privileges and gain full...


Two veteran security experts are launching a startup that aims to help other makers of cybersecurity products to up their game in protecting Apple devices. Their...


ICICI Bank, one of India’s top private banks, exposed the sensitive data of thousands of new credit cards to customers who were not their intended recipients....


Chief Information Security Officers (CISO) are becomingly ever more concerned the increasing use of Generative AI tools could lead to more cybersecurity incidents. A new pape...


Almost a billion mobile users, holding various devices, could have had their communications revealed to malicious third parties, a report from cybersecurity researchers Citizen Lab claims....


Threat actors known as CoralRaider have been using the Bynny content delivery network (CDN) to distribute infostealers to victims around the world. Rresearchers Cisco Talos have...
Last week when a security researcher said he could easily obtain the precise location from any one of the millions of users of a widely used...


Neighbourhood Alert, a messaging app for members in the UK, was leaking sensitive user data to anyone who cared to look, experts have revealed. In the...


Imagine if your antivirus program infected your computer with malware – that’s exactly what happened to some eScan antivirus users recently. A new report from Avast...


In a frankly unsurprising change of course, Google has once again delayed the end of third-party cookies in its Chrome browser. The decision arrives two days...


Automation continues to be a major theme in the enterprise — underscored not least by the rise of AI as a tool to help fix some...


What is the role of the Chief Information Security Officer (CISO)? A new report has suggested it mainly serves as a scapegoat for all cybersecurity incidents,...


UnitedHealth Group has issued an update on the data breach that recently struck its subsidiary, Change Healthcare. The healthcare giant suffered a ransomware attack that knocked...


Production companies such as Amazon, HBO Max and the BBC may be using North Korean labor to produce a number of popular shows, according to the...


Multiple North Korean state-sponsored hacking groups have been attacking South Korean defense companies for more than a year, stealing login credentials and sensitive data. A Reuters...

Russian state-sponsored threat actors were observed abusing an old printer vulnerability to drop custom malware on target endpoints. The malware helped them exfiltrate sensitive data and...


Health insurance giant UnitedHealth Group has confirmed that a ransomware attack on its health tech subsidiary Change Healthcare earlier this year resulted in a huge theft...


A vulnerability in a smart access control system used in thousands of U.S. rental homes allows anyone to remotely control any lock in an affected home....


Hundreds of thousands of WordPress websites are vulnerable to a critical severity flaw which allows threat actors to upload malware to the site through a bug...


The National Security Adviser, Malam Nuhu Ribadu, on Thursday said President Bola Tinubu deliberately appointed northerners into key offices. Ribadu, who spoke in Sokoto, said the...

Prince Harry will not be allowed to appeal the downgrading of his personal security when he visits Britain, a court ruled on Monday. The youngest son...


Israel is closing schools nationwide over security concerns, military spokesman Daniel Hagari said on Saturday, after Iran threatened to retaliate for a deadly air strike on...


Niger State Governor, Mohammed Umaru Bago, has reaffirmed his administration’s unwavering commitment to the security of lives and properties within the state. Making this promise while...

The Arewa Consultative Forum (ACF) has urged Christians to pray for peace, security, and economic recovery for Nigeria during the Easter celebration. In a statement by...

The Assistant Inspector General of Police in charge of Zone 2 Command, AIG Olatoye A. Durosinmi, says he has directed the commissioners of Police in charge...


The Nigeria Security and Civil Defence Corps (NSCDC) has deployed 35,000 personnel to provide security nationwide as Christians celebrate the resurrection of Jesus Christ. This is...


The Martin Luther Agwai International Leadership and Peace Keeping Centre, on Wednesday, rounded off the training of 157 Army troops deployed for a peacekeeping mission to...

The Lagos State Police Command has beefed up security at shopping malls and government warehouses where food items are stored in the metropolis to forestall any...

Mr Muyiwa Adejobi, the Public Relations Officer of the Nigeria Police Force, says the security situation in Nigeria is getting better. “The security situation is getting...


Roadblocks and heavy security were in place around an opposition party’s HQ in Chad’s capital on Thursday, a day after gunfire erupted nearby following a deadly...