

In just over a month, Microsoft will start enforcing multi-factor authentication (MFA) for all Azure administrators. The news was confirmed in a blog post published late...


Experts have identified a way to “confuse” your device when it tries to connect to a trusted Wi-Fi network. As a result, the device is instead...


Cybersecurity researchers from Intego have discovered new variants of the dreaded Cuckoo malware that targets macOS users. For those unfamiliar with the name, Cuckoo is an...


Hackers are stealing people’s DocuSign accounts to make their Business Email Compromise (BEC) attacks seem more authentic, and thus, more successful. A report from cybersecurity researchers...


Kimsuky, an infamous North Korean state-sponsored threat actor, has been using a brand new backdoor to target victims’ Linux devices. Cybersecurity researchers Symantec, who call the...


Hackers have been observed combining spam, a classic IT tech support scam, and Windows built-in remote control and screen-sharing tool, Quick Assist, to deploy the Black...


Sensitive personal data, including Social Security Numbers (SSN), on thousands of Nissan North America (NNA) employees, has been stolen, the company has confirmed. Nissan is only...


BreachForums, one of the most popular clearnet forums for sharing stolen data, malware, and other warez, is thought to have been shutdown by the Federal Bureau...


Some customers of Santander may have had their data stolen following a supply-chain attack targeting one of the bank’s third-party providers. The company confirmed the news...


Icedrive is a cloud storage solution that aims to make cloud storage feel like a physical hard drive with what the company calls “revolutionary” drive-mounting software....


VMware has released patches for four vulnerabilities affecting two of its products. The vulnerabilities could be used by malicious actors to steal sensitive information from flawed...


Meta business accounts are being increasingly hit by cyberattacks, as threat actors look for easy ways to run malvertising campaigns on one of the world’s biggest...


Thousands of Linux servers are still infected by Ebury, a decades-old information-stealing malware that was thought extinct. Ebury is a sophisticated piece of malware designed to...


Security researchers have spotted a new campaign seeking to gain access to corporate networks by targeting macOS devices and employing impersonation/typosquatting on PyPI and steganography to...


Hackers are, once again, pushing out the LockBit ransomware, but this time around, some have been spotted using an old and widely available phishing platform called...


Sensitive Europol data was put up for sale on a dark web forum, but the European law enforcement agency is playing down the importance of the...


Someone is combining information on Chinese citizens leaked in different data breaches into a single database, and has so far made more than 1.2 billion records. ...


Multiple malicious Android applications have been spotted masquerading as some of the platform’s most popular tools, but anyone installing the imposters might get their login credentials...


More than 26 million people have had their personal data exposed on the dark web following a cyberattack on Post Millennial and Human Events. Post Millennial...


In the two years since its inception, the Black Basta ransomware-as-a-service has, through its affiliates, compromised more than 500 organizations all over the world, law enforcement...


Hackers recently tried to scam WPP executives into giving away sensitive information and money. As reported by the Financial Times, the scam was quite elaborate, and...


Modems used in many industrial Internet of Things (IoT) devices can easily be hacked, allowing threat actors root access, remotely and without authentication. The result could...


Using cloud-hosted large language models (LLM) can be quite expensive, which is why hackers have apparently begun started stealing, and selling, login credentials to the tools....


Academic researchers from multiple universities recently discovered a new Spectre-like method of extracting secrets from modern Intel processors. However, Intel says that the original Spectre mitigation...


Popular project management and collaboration tool Monday.com was forced to disable one of its features after it was abused by a threat actor to send out...


Almost a million people around the world have fallen victim to a highly organized fraud campaign, which scammed them out of some $50 million in the...


Boeing has revealed it refused to pay a $200 million ransom demand from ransomware hackers who stole a tranche of sensitive data in 2023. The US...


BIG-IP Next Central Manager (NCM), a centralized management and orchestration platform for F5’s BIG-IP product family, was vulnerable to two major flaws which allowed malicious actors...


American private healthcare giant Ascension suffered a cyber-incursion that forced the company to take parts of its IT infrastructure offline. In a network interruption update posted...


The U.S. Patent and Trademark Office (USPTO) kept an open, internet-accessible database of private postal addresses belonging to patent filers for more than eight months. The...


An older version of LiteSpeed Cache, a popular plugin for the WordPress website builder, is vulnerable to a high-severity flaw that hackers have been increasingly exploiting....


On-demand medical transportation and telemedicine company DocGo has said it recently suffered a cyberattack which resulted in the theft of some sensitive, health-related data. In an...


Brandywine Realty Trust has confirmed suffering a ransomware attack earlier this month, which resulted in the theft of corporate data and the disruption of some parts...


The number of companies suffering ransomware attacks is constantly growing – however, it does seem many are now doing something about it and not just succumbing...


More than half of Tinyproxy service hosts are running a flawed version which hackers could use in remote code execution attacks, a new report from researchers...


Cybersecurity researchers from Leviathan Security have flagged a potentially major security concern around VPN services. The team recently uncovered a vulnerability that forces almost all such...


APT42, an Iranian state-sponsored hacking group also known as Charming Kitten or Yellow Garuda has been spotted impersonating journalists from popular mainstream media titles in an...


The website of ransomware hackers LockBit, which was seized by police and shut down, has relaunched. However, it wasn’t the hackers that propped it back up,...


Businesses have gotten a lot better at spotting cyberattacks recently, but they still struggle to address the problem. As a result, they still suffer the consequences....


Multiple hacking collectives are been actively using Microsoft Graph API to hide their communications with command & control (C2) infrastructure hosted on Microsoft cloud services, cybersecurity...


North Korean state-sponsored threat actors are abusing misconfigurations in DMARC to send convincing phishing emails and gather vital intelligence from Western targets, officials have warned. A...


Microsoft has announced a new, upcoming feature, that aims to solve a decades-old conundrum with DNS security. The feature is called ZTDNS, or Zero Trust Domain...


Hackers have been observed targeting Mac devices running on both Intel and ARM silicon with brand new infostealer malware. Mac security provider Kandji discovered the malware...

We now know how APT28, a known Russian state-sponsored threat actor, managed to compromise multiple email accounts belonging to the Executive Committee of the German Social...
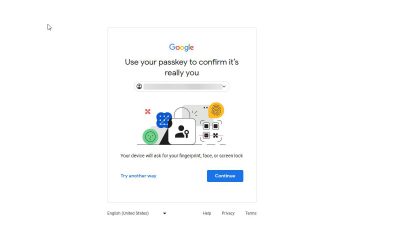

Google is extending its passkeys work in a bid to boost security across the world ahead of a series of major elections, including the US presidential...


Microsoft has just unveiled the next step in its major cybersecurity overhaul, and that is to hire security executives for different product groups. Following a string...


The U.S. Cybersecurity and Infrastructure Security Agency (CISA), and the Federal Bureau of Investigation (FBI), published a new joint security alert earlier this week, urging software...


Cybersecurity researchers from Microsoft found a way for Android malware to overwrite files in another, legitimate application’s home directory. In theory, threat actors could use this...


E-signature service providers DropBox Sign suffered a cyberattack recently, in which hackers stole some seriously sensitive customer information. As per the data breach notification published on...

When hackers find a vulnerable router, they compromise it by installing malware that grants persistence, the ability to run distributed denial of service (DDoS) attacks, hide...


Cybersecurity researchers from JFrog recently discovered three malicious campaigns in Docker Hub – Docker’s cloud-based registry service for storing and sharing container images. These campaigns contained...


Chinese state-sponsored actors are apparently mapping out the entire internet, but it’s hard to determine why. Some media speculate that it might be in preparation for...


To break into Change Healthcare’s IT systems, hackers abused a vulnerability in a Citrix remote desktop access product. This is according to Andrew Witty, Chief Executive...


An American debt collection agency suffered a data breach in late February, losing sensitive data belonging to almost two million people. Earlier this week, Financial Business...


Canadian retail pharmacy chain London Drugs experienced a cyber-incident which forced the company to temporarily shut down its stores across Western Canada. On Sunday night, the...


Fake USPS websites, designed to steal people’s sensitive information and payment data through phishing, get almost as much traffic as the actual USPS website. During the...


Software developers are being targeted, once again, by fake job ads. The goal of the newly observed campaign is the same as the ones seen before...


Identity and access management company Okta says it is facing an “unprecedented” scale of credential stuffing attacks, looking to breach user accounts of its online services. ...


Spy.pet, a website that offered billions of Discord chat logs for sale, has been taken offline by the chat app provider. Discord accounts associated with the...


Despite security experts constantly warning about the risks of reusing passwords, a shockingly high number of people still do just that – and to make matters...


Millions of devices are still connected to the PlugX malware, despite its creators abandoning it months ago, experts have warned. Cybersecurity analysts Sekoia managed to obtain...


A critical vulnerability recently discovered in a popular WordPress plugin, is being actively abused in the wild, researchers have said, with hackers potentially able to use...


IT security pros are not the only ones with sandboxes and honeypots to test malware in, as hackers are doing the same – in developing parts...
A popular phone tracking app was found to be leaking sensitive data on millions of its users. A security researcher named Eric Daigle discovered the flaw...


Network monitoring and security solution Progress Flowmon was found to be carrying a maximum-severity vulnerability which could allow threat actors to escalate privileges and gain full...


Chief Information Security Officers (CISO) are becomingly ever more concerned the increasing use of Generative AI tools could lead to more cybersecurity incidents. A new pape...


Almost a billion mobile users, holding various devices, could have had their communications revealed to malicious third parties, a report from cybersecurity researchers Citizen Lab claims....


Threat actors known as CoralRaider have been using the Bynny content delivery network (CDN) to distribute infostealers to victims around the world. Rresearchers Cisco Talos have...


Neighbourhood Alert, a messaging app for members in the UK, was leaking sensitive user data to anyone who cared to look, experts have revealed. In the...


Imagine if your antivirus program infected your computer with malware – that’s exactly what happened to some eScan antivirus users recently. A new report from Avast...


What is the role of the Chief Information Security Officer (CISO)? A new report has suggested it mainly serves as a scapegoat for all cybersecurity incidents,...


UnitedHealth Group has issued an update on the data breach that recently struck its subsidiary, Change Healthcare. The healthcare giant suffered a ransomware attack that knocked...


Multiple North Korean state-sponsored hacking groups have been attacking South Korean defense companies for more than a year, stealing login credentials and sensitive data. A Reuters...

Russian state-sponsored threat actors were observed abusing an old printer vulnerability to drop custom malware on target endpoints. The malware helped them exfiltrate sensitive data and...


Hundreds of thousands of WordPress websites are vulnerable to a critical severity flaw which allows threat actors to upload malware to the site through a bug...